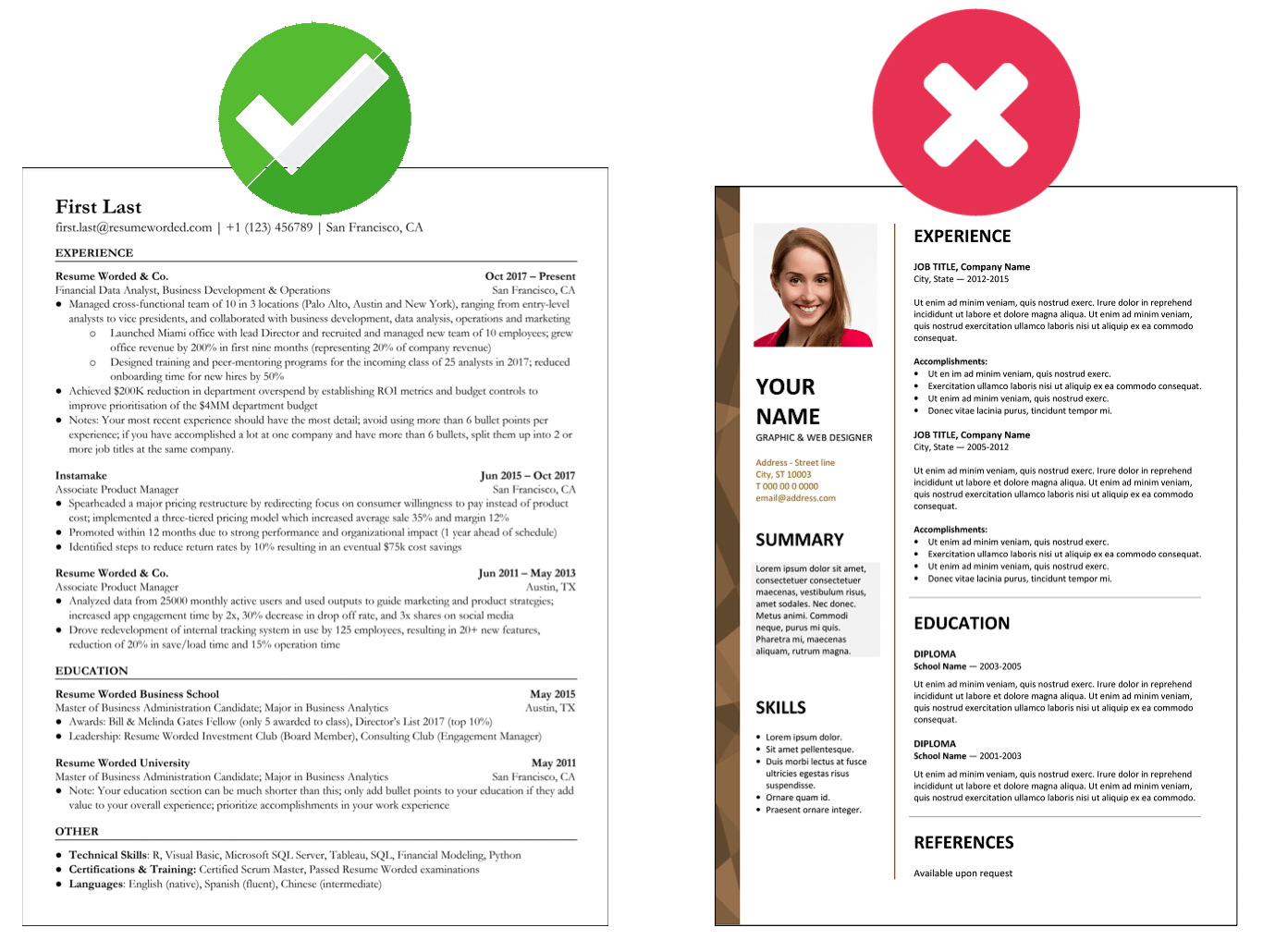
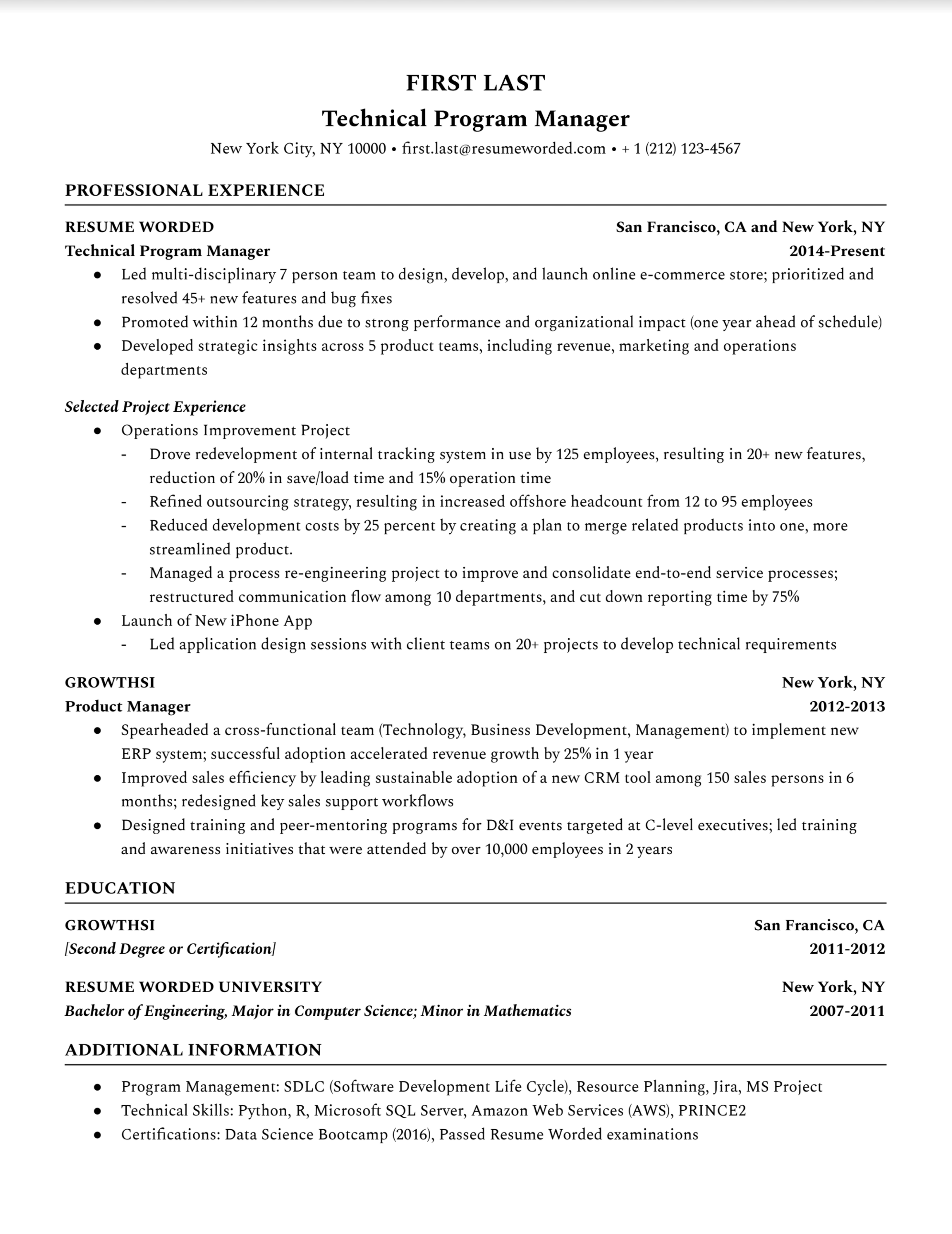
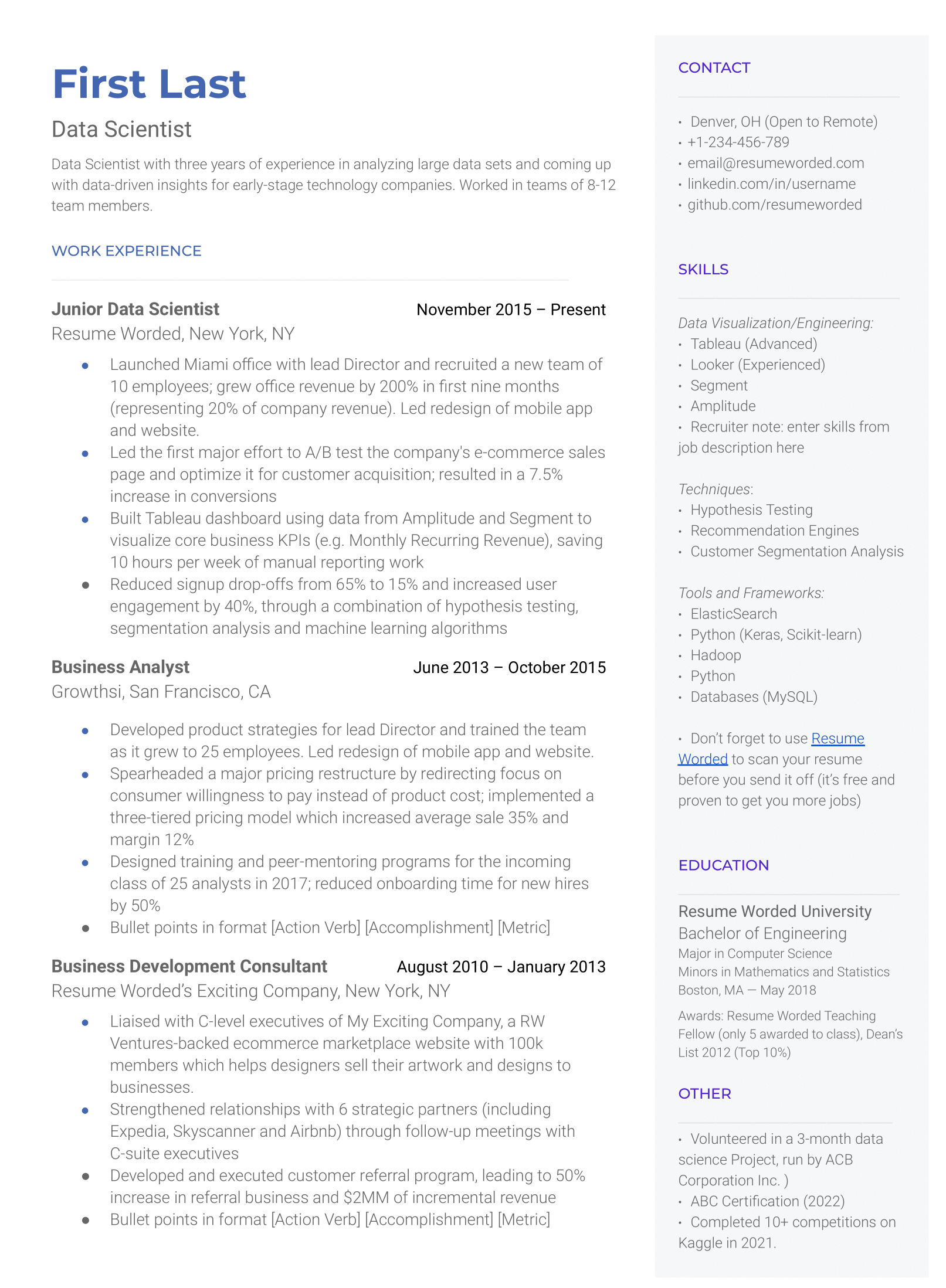
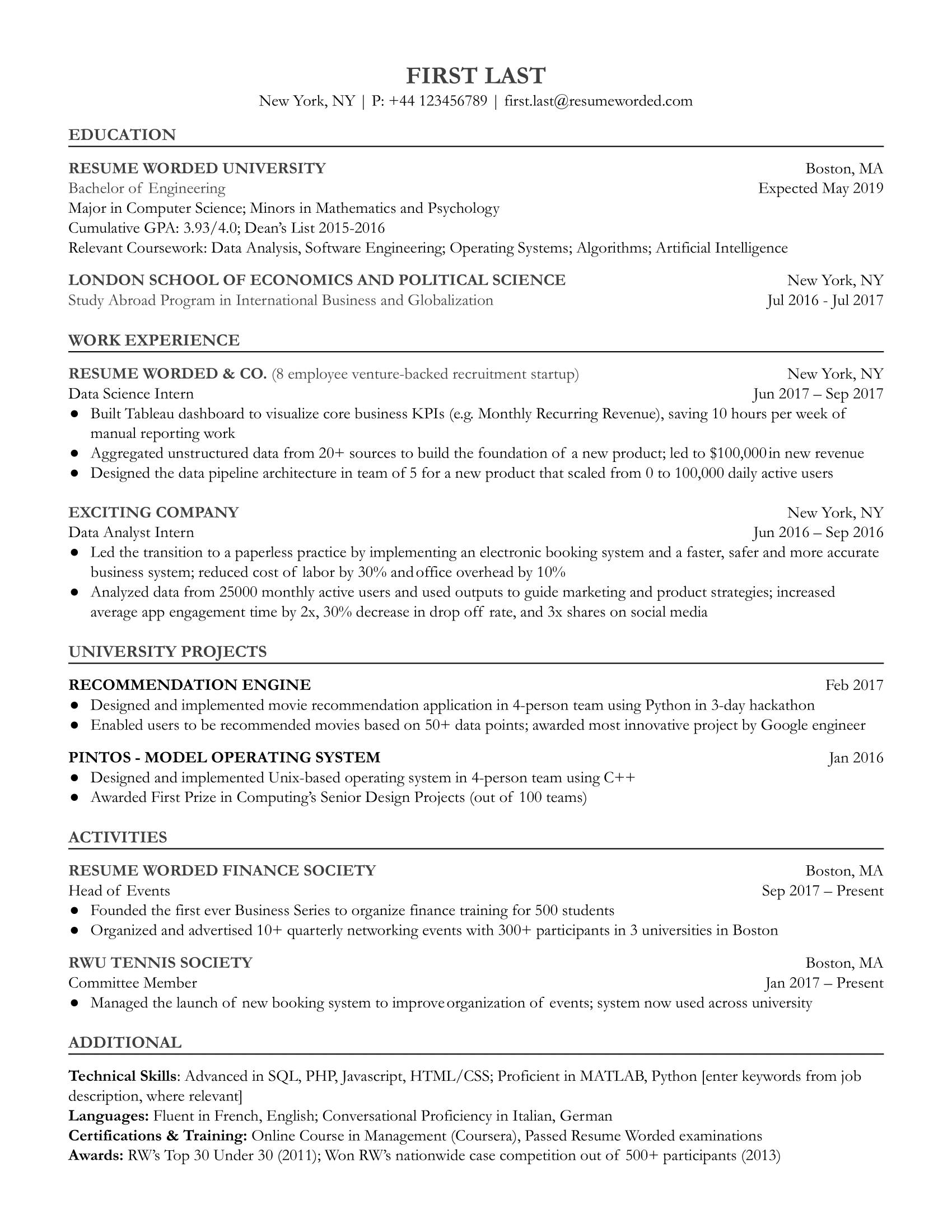
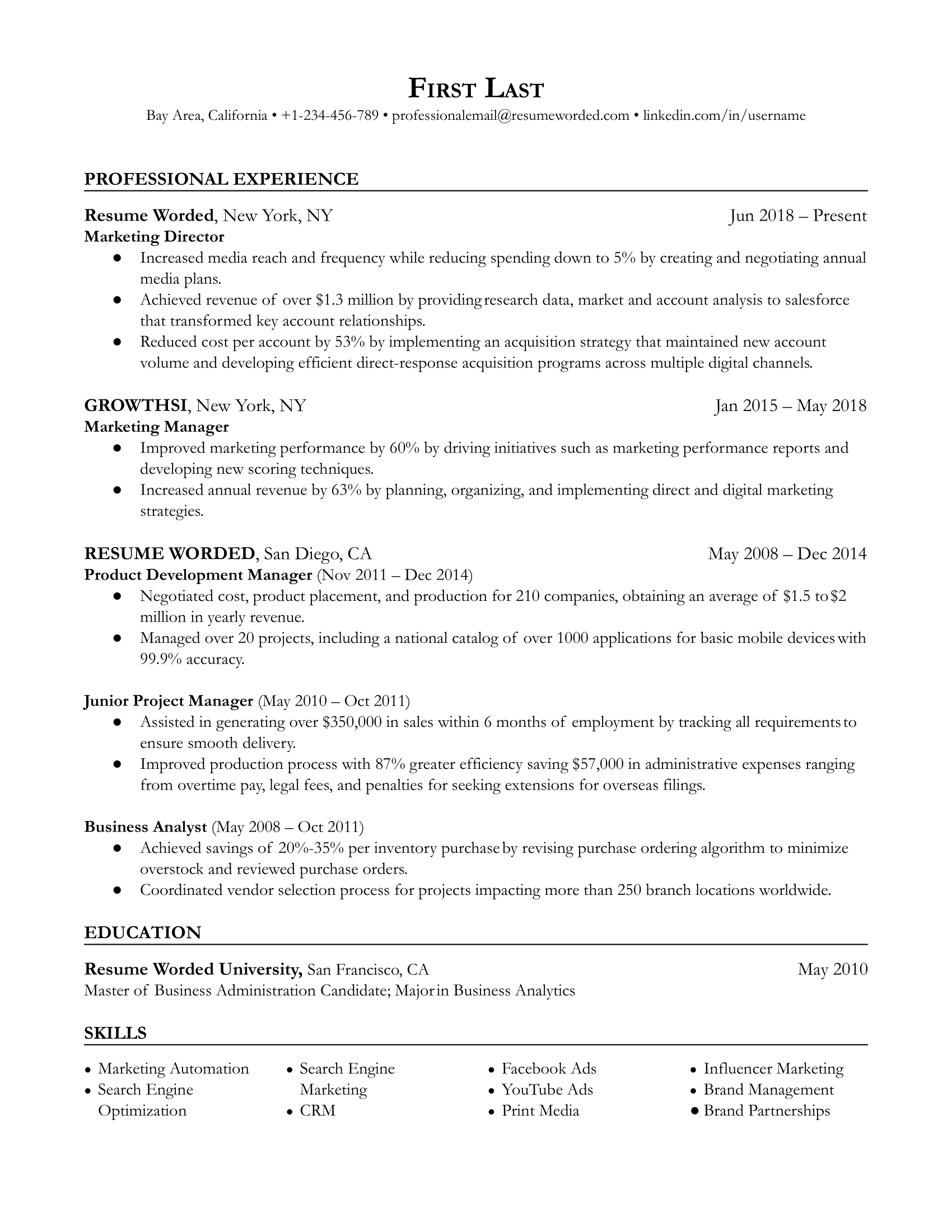
Makes great use of space
It strikes the right balance between white space and content, and doesn't waste space on unnecessary images and icons. Remember, recruiters aren't looking at how creative you are when it comes to your template. Your content is core and should be the focus.